Let’s Be Safe Out There…In Three Easy Steps
 Back in the 80’s the crime drama Hill Street Blues popularized the phrase “Let’s Be Safe Out There.” As is common in most police departments, the officers of Hill Street attended a squad meeting prior to starting the next shift. The show regularly began at this briefing where their gruff, no-nonsense Sergeant, Phil Esterhaus, would give them their daily instruction. It ended with “Let’s be safe out there.” That’s a fitting title for this Ministry Resource post as each and every day in this internet age you embark on a “shift” that could see untold disasters — computer viruses, data corruption, ransomware, identity theft. You need to be ever vigilant. Fortunately it isn’t that hard to “stay safe out there.” I’ve condensed it down to three easy steps to protect yourself and your ministry activities.
Back in the 80’s the crime drama Hill Street Blues popularized the phrase “Let’s Be Safe Out There.” As is common in most police departments, the officers of Hill Street attended a squad meeting prior to starting the next shift. The show regularly began at this briefing where their gruff, no-nonsense Sergeant, Phil Esterhaus, would give them their daily instruction. It ended with “Let’s be safe out there.” That’s a fitting title for this Ministry Resource post as each and every day in this internet age you embark on a “shift” that could see untold disasters — computer viruses, data corruption, ransomware, identity theft. You need to be ever vigilant. Fortunately it isn’t that hard to “stay safe out there.” I’ve condensed it down to three easy steps to protect yourself and your ministry activities.
Step One: Use a cloud backup service.
The absolute best way to protect yourself from many of the data disasters that can strike your computer is by having an up-to-the-minute backup of all your data. A couple of weeks ago I talked about cloud services like Google Drive and OneDrive that can sync your data between a local copy on your computer and one in the cloud. This is a great productivity approach, but it is not protection against data loss or corruption. You need a bonafide backup solution.
One of the hardest things about backups is remembering to do them. That is why I prefer cloud backup solutions that just work in the background and normally don’t need any intervention by you. They just hum along waiting for files to be changed or added, then they copy them up to the cloud server. They automatically will keep different versions of those files, so you can go back in time to grab an older copy, or even the contents of your entire disk.
The service I almost always recommend is Backblaze. It just works. It is relatively inexpensive, about $60/year. And it is one of the only ones that will backup everything on your hard drive AND all connected drives like external hard drives or even flash drives.
Step Two: Encrypt your data.
While step one will allow you to restore your data should it become corrupt, your hard drive fails, or someone is holding your data hostage for a ransom fee (it happens more than you think), what if somebody steals the data on your disk, or your entire computer for that matter? In that data could be passwords, social security numbers, tax returns, etc. All information that could be sold and used for identity theft or other illegal activities that would be hard to recover from.
The best way to keep that data safe wherever it may go is to encrypt it. While that sounds hard and techy, today’s operating systems like Windows 10 and Mac OS make it surprisingly easy. Encryption is the conversion of electronic data into another form which cannot be easily understood by anyone except authorized parties with the encryption password or key. Normally the process requires you to provide a master password, then the operating system takes that password and creates “encoded” content, that only a system with your key or password can decode. If you want to learn more read the article “What is Encryption, and Why Are People Afraid of It.”
The best way to encrypt the contents of your hard drive is to use the built in encryption tools. For Windows it is called “Bitlocker.” On the Mac it is “FileVault.” Once you start the process, it should busy itself in the background for a while. It may take a while depending on how many files you have. When done you will probably never notice it unless you need to do some kind of recovery process. Don’t forget the key/password you set.
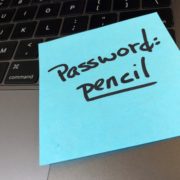
Step Three: Use a password manager.
We’ve discussed how to secure the data that is on your physical device. By the way most phones and tablets these days are already encrypted, so no worries on that front. But what about all those cloud services you use — your banking website, credit cards, your church or school information systems? That is stuff you don’t want to have any unauthorized access to. But if your username and password are stolen, the door is wide open.
To truly protect your online activities you should have a different password for every cloud-based service you use. That becomes very impractical very fast as almost everything is now online. That still does not justify having the same password for any two sites. Fortunately there are tools to help. In my opinion LastPass stands at the top of the heap. It is easy to use, cross platform (PC, Mac, Android, iOS), and has some great features like strong password generation, password sharing, local copy availability, and two factor authentication. To get the mobile version, which you should, will cost $12/year. If you want to have everybody in your organization use it, you might want to investigate the enterprise version, which costs about $17/person/year for non-profits (at least the last time we renewed our licenses). A worthy investment.
These kind of tools are easy to operate. They usually just sit as an extension or add on to your browser, and when you are creating new online accounts that require passwords, they spring into action and ask if you’d like to auto-generate a strong password. Say yes! Also, when you then visit a site that you have previously stored in LastPass, for instance, it will pre populate your username and password, and you’re in! Like the encryption password, you MUST remember your LastPass password. However, it’s a lot easier to remember one password than hundreds.
So for less than $100 per year you can experience all the benefits of the tools mentioned and have a higher level of confidence that your data will be safe and available. After all, you have better things to think about and do than spend more time fighting to keep your information safe. Let technology work for you. You go ahead and work for the Lord. And, oh yeah, let’s be safe out there!
Related resources
I gave you recommendations above for each of the three steps, however there are other equally capable tools in each category. If you’d like to comparison shop:
Cloud Backup Solutions: Carbonite, MozyHome, Google Backup & Sync
Encryption: There really is no reason to stray from encryption built into your computer, however older PC hardware may not have a TPM chip in it. You can still use BitLocker however, it’s just not as foolproof as those systems that do have this hardware encryption chip. You will be notified if you do or don’t during the BitLocker installation process. There are alternatives however. Last year I would have recommended TrueCrypt, but that is no longer supported. Here is a good article on similar free products.
Password Managers: 1Password, Keeper, Sticky Password
Google Backup and Sync is a relatively new service that holds promise. I’ve included a YouTube video that was recorded by VerySlowPC.com that shows the differences between this new solution and the old Google Drive.









Leave a Reply
Want to join the discussion?Feel free to contribute!